When GitHub Actions Goes Down: CI Resilience Lessons (2026)
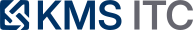
Recent GitHub Actions incidents highlight a hard truth: hosted CI is a dependency. Here’s how to design pipelines so outages degrade gracefully instead of freezing delivery.
KMS ITC
Hosted CI is convenient—until it becomes your single point of failure.
GitHub’s status page has documented multiple recent incidents affecting Actions and adjacent systems (webhooks, PR workflows, Copilot). The details matter, but the meta-lesson is simple:
If your delivery pipeline can’t tolerate a CI outage, your delivery pipeline isn’t a pipeline—it’s a dependency.
1) Executive summary
- Expect CI outages. Design for “degraded mode,” not “perfect uptime.”
- Separate feedback from release. PR checks can be slow; releases should still be possible with explicit controls.
- Have a fallback compute plan. Even a small self-hosted runner pool can turn a full stop into a slowdown.
2) What changed
GitHub’s status page describes incidents such as:
- hosted runners becoming unavailable, causing Actions jobs to queue and time out
- follow-on impact to other features that rely on Actions compute
- delays in webhooks and workflow starts/status updates
3) Why it matters
CI/CD is not “just tooling.” It is part of your production system.
When Actions is degraded, teams typically experience:
- deployment freezes (no pipeline, no release)
- slow PR feedback (review + merge bottlenecks)
- cascading delays (webhooks, status updates, integrations)
The business risk isn’t the outage itself—it’s that your org has no safe manual or alternate path to deliver changes.
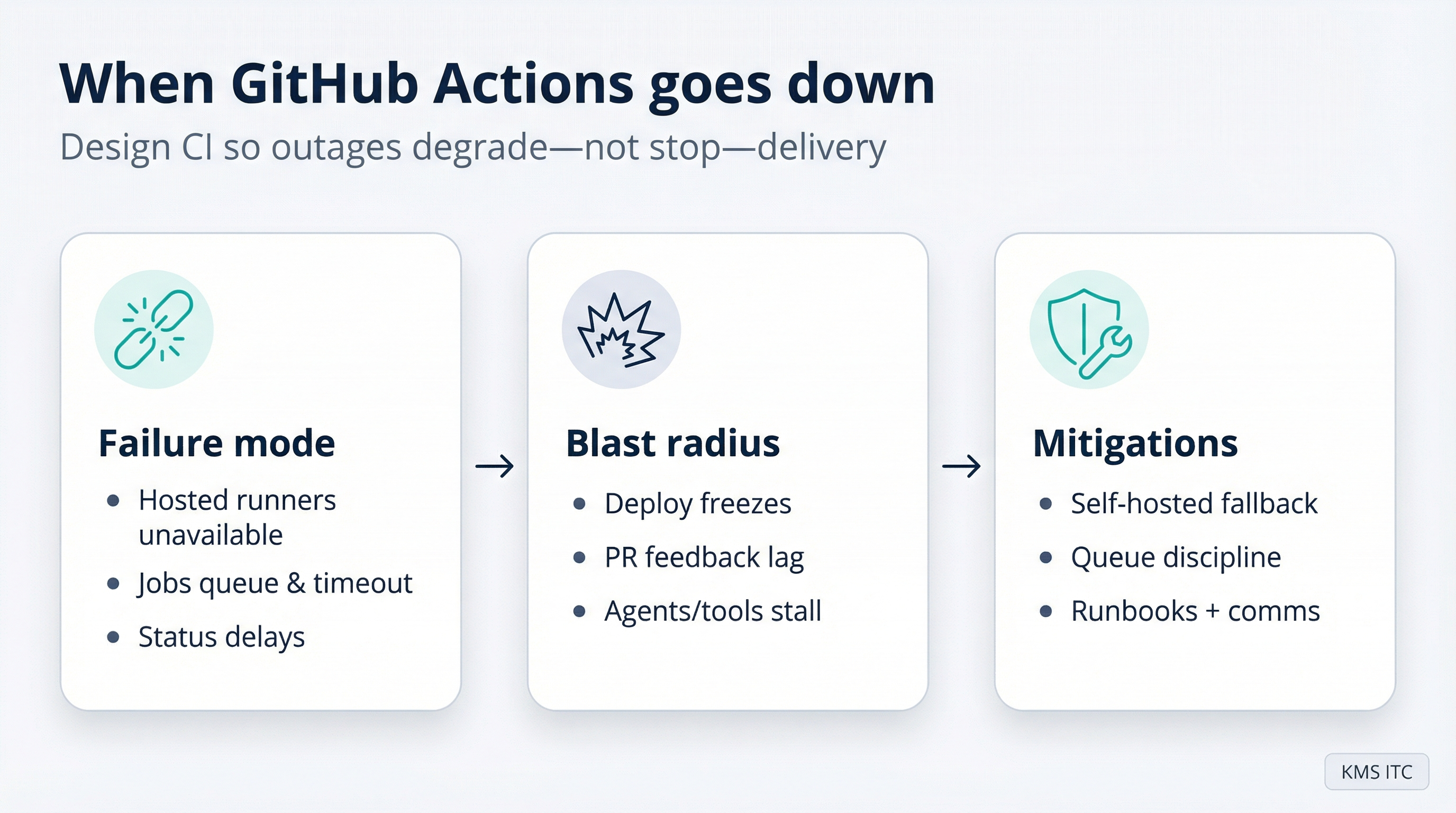
4) What to do (checklist)
4.1 Fallback compute
- Stand up a minimal self-hosted runner pool for critical workflows (release, hotfix).
- Keep the runner image boring: pinned toolchains, cached deps, reproducible builds.
- Document the switch-over runbook and test it quarterly.
4.2 Queue discipline
- Use concurrency limits and cancel redundant runs (especially on force-push heavy repos).
- Treat timeouts/retries as capacity controls, not as afterthoughts.
4.3 Delivery flow
- Split workflows:
- PR feedback (fast, safe, minimal permissions)
- deployment (protected environments, explicit approvals)
- Be able to ship with a controlled override when CI is degraded.
4.4 Observability and comms
- Alert on: queue time, runner acquisition time, workflow start latency.
- Make “CI status” visible to engineering leadership.
- Establish a simple comms ritual during incidents (what’s impacted, what’s paused, what’s the fallback).
5) Risks / tradeoffs
- Self-hosted runners increase operational responsibility.
- Fallback paths can be abused if you don’t lock down permissions.
- Over-optimising for outages can add complexity—keep the fallback minimal.
Sources
- GitHub Status (Actions/PR incidents and summaries): https://www.githubstatus.com/
- GitHub Actions updates (platform changes and controls): https://github.blog/changelog/2026-02-05-github-actions-early-february-2026-updates/