SmarterMail CVE-2026-24423: The KEV Signal MSPs Can’t Ignore
CISA says CVE-2026-24423 is being used in ransomware campaigns. If you run SmarterMail (especially for customers), treat this as an exposure + patch + verification exercise — not a ‘we’ll catch it next cycle’ update.
KMS ITC
Executive summary
- CVE-2026-24423 is in CISA’s KEV catalog and marked “Known to be used in ransomware campaigns.” That’s your prioritisation shortcut: treat it as actively exploited, not theoretical.
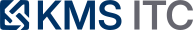
- The failure mode is operationally dangerous: an unauthenticated API path can be chained into OS command execution, which is exactly the kind of foothold ransomware operators love.
- The practical win is fast: patch to a fixed build, reduce exposure of admin/API surfaces, then verify in logs that nobody already touched the endpoint.
What changed
Over the last few days, three things tightened the screws for defenders:
-
CISA added CVE-2026-24423 to the Known Exploited Vulnerabilities (KEV) catalog (date added: 2026-02-05, due date: 2026-02-26) and explicitly notes it is known to be used in ransomware campaigns.
-
Reporting indicates the issue affects SmarterMail versions prior to a fixed build and can lead to unauthenticated remote code execution via the ConnectToHub API workflow.
-
The bigger pattern: SmarterMail has seen a cluster of high-impact bugs recently. Even if you patched one earlier item, you should assume you’re not “done” unless you’re on the latest build and have constrained exposure.
Why it matters
SmarterMail is commonly deployed by MSPs and hosting providers because it’s self-hosted, Windows-based, and cost-effective. That’s also why this is a high-stakes bug:
- A single exposed mail server can be a customer-impact multiplier. Ransomware operators don’t need to “own everything” — they need one reliable entry point to start credential theft, lateral movement, and encryption.
- Email servers sit at a uniquely sensitive intersection: authentication, tokens/sessions, directory integration, and high-volume external input.
- KEV changes your decision math. “We’ll patch next maintenance window” is sometimes a reasonable tradeoff for low-signal CVEs. It’s hard to justify when the signal is: exploited in the wild.
What to do (checklist)
Use this as a pragmatic 24–48 hour plan.
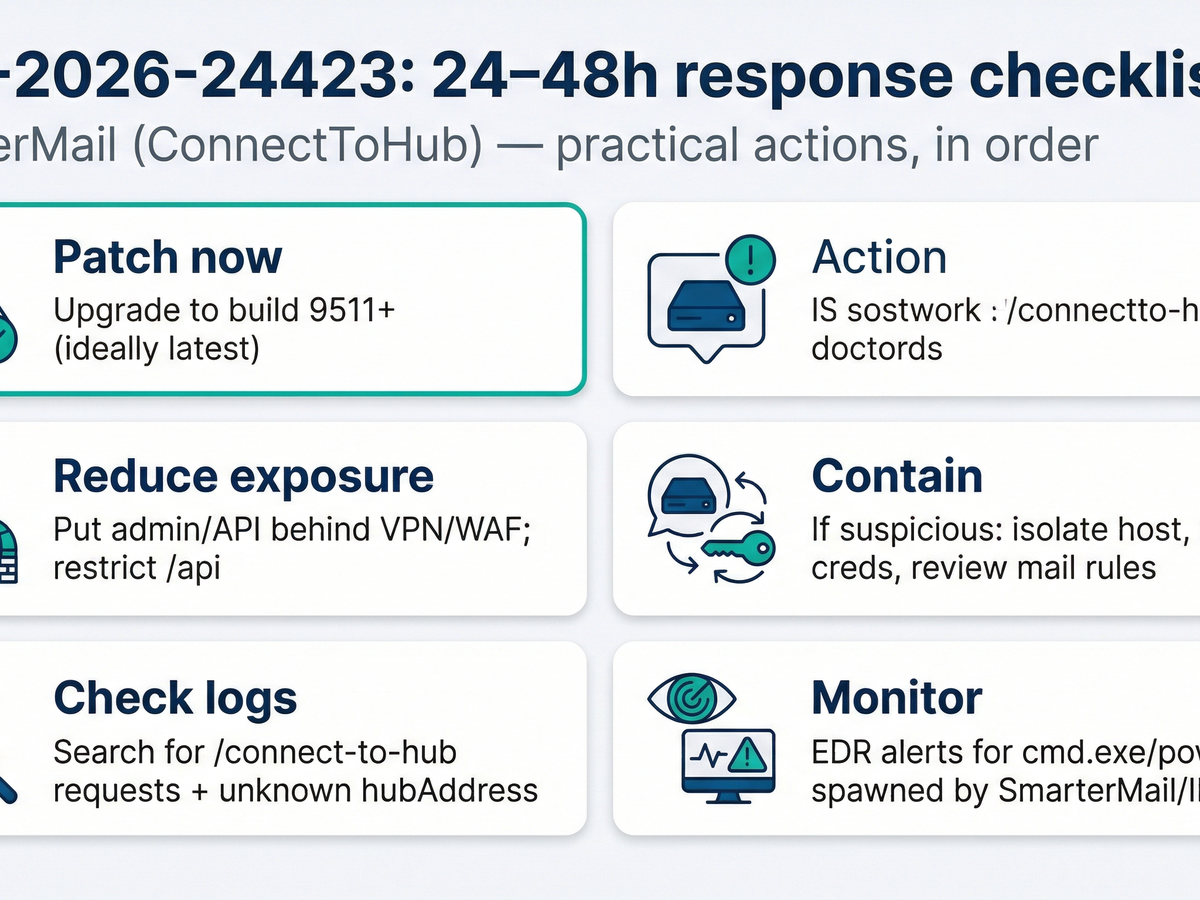
1) Patch (and standardise)
- Upgrade SmarterMail to a fixed build (minimum fixed build referenced publicly is 9511; prefer the latest current build).
- If you manage multiple instances (MSP/hosting): standardise on a “golden” SmarterMail build and roll forward as a fleet, not as one-offs.
- Capture evidence: version/build number, install time, and the list of affected hosts.
2) Reduce exposure of the risky surface
- Put admin and API paths behind a VPN, allowlist, or WAF (even if the webmail UI must remain public).
- Ensure management interfaces are not directly Internet-reachable.
- If you can’t restrict fully, at least add rate limiting + geo/IP allowlists for admin/API endpoints.
3) Verify you weren’t already hit (logs first, then EDR)
- Search for suspicious interactions with the ConnectToHub endpoint (commonly reported as:
/api/v1/settings/sysadmin/connect-to-hub). - Look for unfamiliar
hubAddressvalues or unexpected outbound requests triggered by SmarterMail. - On the host, review process ancestry for signs of command shells spawned by the SmarterMail/IIS worker context.
4) If you find anything suspicious: contain like it’s real
- Isolate the host (network containment beats “quick cleanup”).
- Rotate credentials that could be exposed from the server (service accounts, admin creds, API keys).
- Review mail rules/forwarders and admin account changes.
Risks / tradeoffs
- Urgent patching can break service. Email downtime is painful; ransomware is worse. The tradeoff most teams make successfully: patch in a tight, announced window with a rollback plan.
- Restricting admin/API access can create operational friction (especially for MSPs). The counter-tradeoff is designing a secure management path (VPN + bastion + allowlists) once, then scaling it.
- Hunting without context can generate noise. Start with a narrow set of high-signal pivots: the specific endpoint, unusual
hubAddress, and unexpected child processes.
Sources
- CISA — Known Exploited Vulnerabilities Catalog entry for CVE-2026-24423: https://www.cisa.gov/known-exploited-vulnerabilities-catalog
- BleepingComputer — CISA warns of SmarterMail RCE flaw used in ransomware attacks: https://www.bleepingcomputer.com/news/security/cisa-warns-of-smartermail-rce-flaw-used-in-ransomware-attacks/
- Help Net Security — Ransomware attackers exploiting critical SmarterMail vulnerability (CVE-2026-24423): https://www.helpnetsecurity.com/2026/02/06/ransomware-smartermail-cve-2026-24423/