Enterprise Architecture
MCP Toolbox Java SDK: the control-plane pattern for transactional enterprise agents
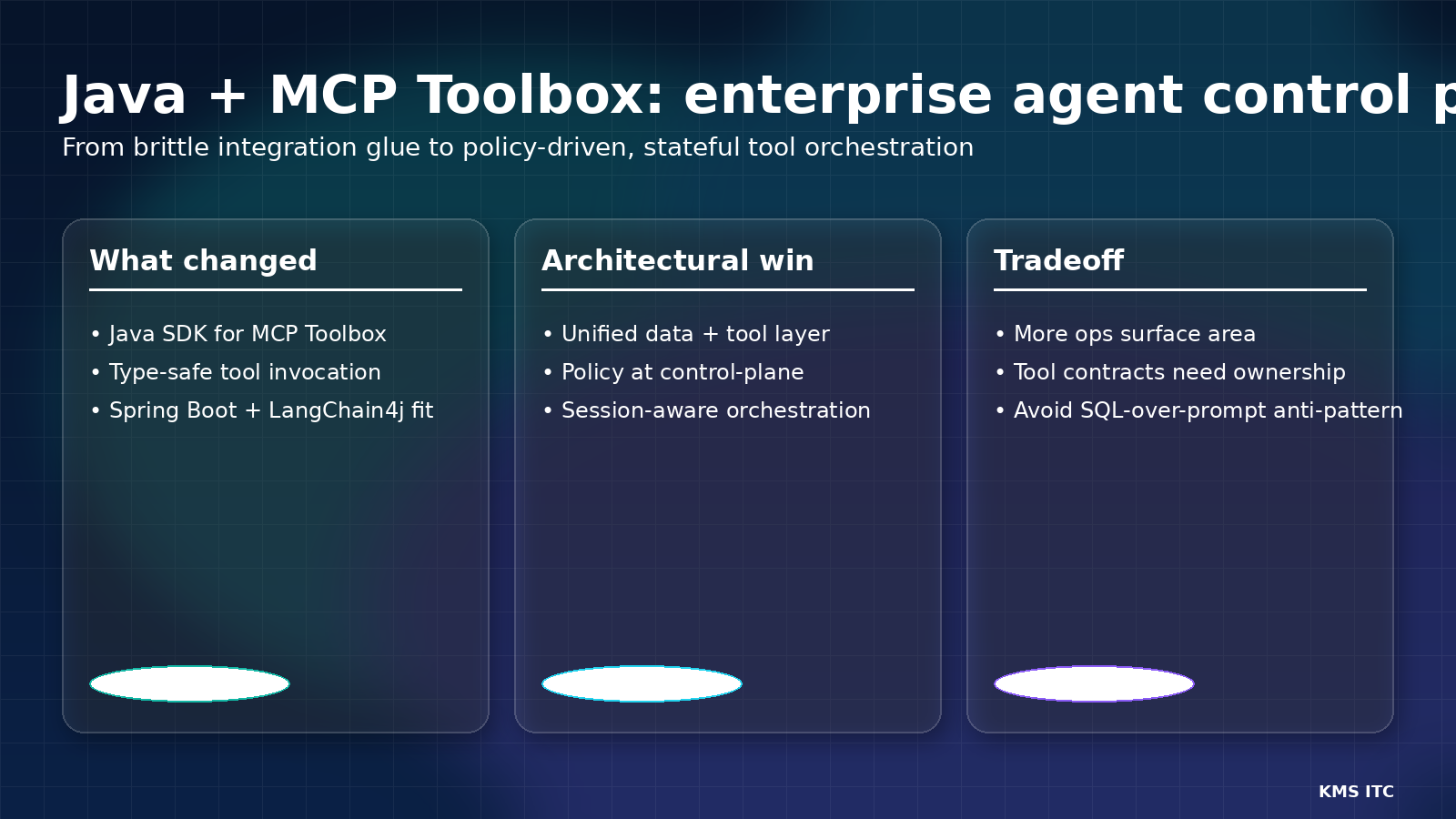
Google’s MCP Toolbox Java SDK signals a practical architecture shift: move from custom integration glue to a policy-driven agent control plane where tool contracts, identity, and governance are first-class.
Most enterprise AI teams don’t fail at model calls.
They fail in the gap between model output and system-of-record execution:
- too much brittle glue code,
- unclear ownership of tool contracts,
- and weak policy controls around state-changing actions.
Google’s MCP Toolbox Java SDK matters because it points to a cleaner pattern: treat agent tool access as a governed control plane, not a collection of one-off integrations.
1) What changed
The release combines several enterprise-relevant elements:
-
Java SDK for MCP Toolbox for Databases
- Type-safe discovery and invocation of tools from Java/Spring apps.
-
Tool abstraction over many data sources
- MCP Toolbox positions tools as controlled interfaces above database operations, with support for many backends.
-
Security and runtime primitives built in
- Patterns such as parameter binding and environment identity (ADC) reduce hardcoded credential and prompt-to-SQL risk.
On paper, this sounds incremental. Architecturally, it is a major operating-model opportunity.
2) Why this matters for CTOs and architects
A) It formalises the missing layer between LLM and database
Many agent projects jump straight from prompt to SQL/API calls.
A control-plane approach inserts explicit governance:
- what tools exist,
- what each tool can do,
- who can invoke it,
- and how calls are audited.
That is how you scale beyond pilots.
B) It fits enterprise Java reality
In large organisations, critical systems are still deeply Java-centric.
A Java-native SDK lowers adoption friction for teams already running:
- Spring Boot services,
- transaction-heavy workloads,
- and existing observability/identity standards.
C) It improves Day-2 operability
When agents become production systems, Day-2 concerns dominate:
- concurrency,
- retries/backpressure,
- session continuity,
- and policy drift.
The control-plane model gives platform teams a single place to standardise these concerns.
3) The core architecture pattern
Use a three-layer model to keep agent intent cleanly separated from data-layer execution:
Three-layer reference architecture:
┌─────────────────────────────────────────────┐
│ Layer 1: Agent Runtime │
│ LLM + planning + memory/session context │
└──────────────────────┬──────────────────────┘
│ tool calls
┌──────────────────────▼──────────────────────┐
│ Layer 2: MCP Control Plane │
│ Tool registry │ AuthZ │ Budgets │
│ Evaluation gates │ Trace IDs │
└──────────────────────┬──────────────────────┘
│ parameterized requests
┌──────────────────────▼──────────────────────┐
│ Layer 3: Data / Tool Adapter │
│ Parameterized SQL │ Enterprise APIs │
│ Transactional boundaries │
└─────────────────────────────────────────────┘| Layer | Owns | Enforces |
|---|---|---|
| Agent runtime | Goals, planning, context | Conversation scope |
| MCP control plane | Tool contracts, access policy | AuthZ, budgets, audit trail |
| Data/tool adapter | Data access, transactions | Input binding, backend safety |
This separation is what keeps you out of the “prompt directly controls production data” trap.
4) Tradeoffs you need to manage
Tradeoff 1: More platform surface area
A real control plane introduces governance components and lifecycle overhead.
Mitigation: start with a small, opinionated tool catalog and strict onboarding checklist.
Tradeoff 2: Tool schema quality becomes a bottleneck
If tool definitions are ambiguous, type safety alone won’t save you.
Mitigation: assign clear tool owners and require contract tests plus failure-mode tests.
Tradeoff 3: Stateful agents can hide risky coupling
Session memory can unintentionally leak assumptions across workflows.
Mitigation: classify context scopes (user/session/workflow), enforce expiration, and log attribution.
5) What to do next (30/60/90)
30 days
- Identify top 10 state-changing agent actions.
- Wrap them as explicit tools with input constraints and owner metadata.
- Add policy tags (risk tier, data sensitivity, allowed caller).
60 days
- Implement centralized authz + request budgets for tool calls.
- Add trace correlation from user intent → tool invocation → data mutation.
- Define blocking evaluation gates for high-risk tools.
90 days
- Publish a self-service internal tool catalog with governance defaults.
- Add reliability patterns: queue limits, retries, compensation flows.
- Review drift monthly: cost, latency, policy violations, failed tool calls.
Sources
- Google Cloud Blog: MCP Toolbox Java SDK
- MCP Toolbox documentation
- Java SDK repository
- Cymbal Transit reference app
If you want a one-page enterprise rollout blueprint (tool taxonomy, policy gates, and evaluation checklist), reach out via /contact and include your primary cloud and whether your first use case is read-only copilots or transactional automation.